Purpose of the solution
The solution is designed for software solutions in indusry and public management.
Functions of COSOC.BG
receiving and recording messages from subjects (various DDS, utilities, citizens, etc.) and objects (SCADA systems, video cameras, etc.) in a centralized or decentralized storage;
displaying information about messages both on the map base and in the list (news feed) in accordance with the selected rules;
processing messages according to pre-configured algorithms and rules; calculation and display of key indicators describing the current situation in the areas of activity of the monitoring object;
recognition and assessment of the current situation based on the received messages; selection of the proposed response plan based on the accumulated database;
modeling of the current situation (simulation, dynamic, etc.) with the possibility of answering the question "What will happen if" and "What would happen if";
formation of a database of response plans; displaying the location of critical infrastructure objects, forces and means on the map base;
displaying the general picture of the situation of a specific situation
Data Sources
Information about events and threats comes from external sources (subjects or objects) in the Common Alerting Protocol (CAP, General Alert Protocol) format. CAP is an xml format supported by the Organization for the Development of Structured Information Standards (ORSSI), as well as defined in Recommendation ITU-T X.1303.
As sources of information can be used:
- mobile devices that allow citizens to report events and threats; stationary devices "alarm button";
- serviced and unattended sensor systems (transport, meteorological, environmental, special...);
- intelligent video surveillance systems; dispatcher services on duty;
- external systems that transmit information through interdepartmental communication channels (including international ones);
- mass media, telegraph agencies; public services.
Solution description
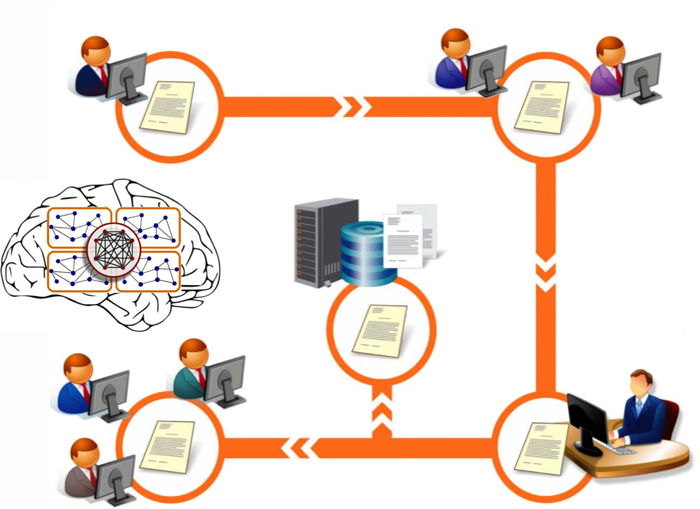
Incoming message formats, rules and algorithms for message processing, formulas for calculating key indicators, methods for recognizing typical situations, predictive models, descriptions of forces and means are developed as part of models of each subject area (type of activity) described in COSOC sets of xml files. COSOC is built on the basis of a service-oriented architecture, the main element of which is an Integration Platform for interaction with external data sources, as well as related systems. Information from CAP messages is extracted in accordance with the exchange regulations, grouped, if necessary, after which it is processed according to algorithms and methods previously laid down in COSOC at three hierarchical levels, in accordance with the IBM Component Business Model proposed: 1) the level of direct response to the event; 2) the level of tactical decision-making on situations; 3) the level of strategic decision-making. Incoming information is processed
Information environment
To ensure calculations, algorithms and working methods, the following information support is provided in COSOC:
1. A directory of CAP messages, including a description of message types and codes, a list of external sources linked to these types of messages.
2. A directory of external sources of messages, including a description of the types of sources, as well as parameters of the protocols of exchange with them, including methods of constructing requests to them and characteristics of the generated requests.
3. The KPI classifier, which describes, in fact, the model of the subject area, including, among other things, algorithms for calculating KPI, threshold values.
4. A codifier of typical tactical situations containing a list of typical tactical situations, a list of KPI values, single and group CAP messages by which the situation can be recognized, a list of requests for additional information from external sources (or manually entered), as well as formalized criteria for evaluating the entire set of parameters.
5. A register of Response Plans containing a detailed list of measures for each Plan, linked to the Forces and Means that are involved in their implementation.
6. Directory of Critical Infrastructure Objects, including a passport of the object indicating the geographical coordinates of the location of the object;
7. A directory of types of Forces and Means containing descriptions of the types of resources, both human and technical, that are involved in the implementation of Action Plans.
8. Passports of Forces and Means describing the real situation with the availability and arrangement of resources, according to the Directory of Forces and Means.
9. Technical conditions (technical specifications) for the interaction of external data sources and related systems, which regulate the exchange of information.
Pubications
Применение нейросетевых технологий для автоматической классификации и маршрутизации текстовых сообщений и документов в работе ЕЦОР и служб эксплуатации и ремонта
Хельвас А.В., Овчинников А.Д., Кузнецова А.А., Гиля-Зетинов А.А.
в сборнике ”Имитационное и комплексное моделирование морской техникии морских транспортных систем” Материалы пятой международной научно - практической конференции ИКМ МТМТС-2019, место издания М: ”Издательство Перо”, с. 191-196
The software platform and information model of a situational center
S.S.Shcherbakov, A.A.Kuznetsova, A.A.Bespalko, A.S.Galitskiy, A.V.Khelvas
Trudy MFTI 2018 v.10 №4(40) pp.98-109
Practical usage of Alloy for tactical situations recognition
A.V. Khelvas, A.B. Galitskiy
Trudy MFTI 2018 v.10 №4(40) pp.87-97